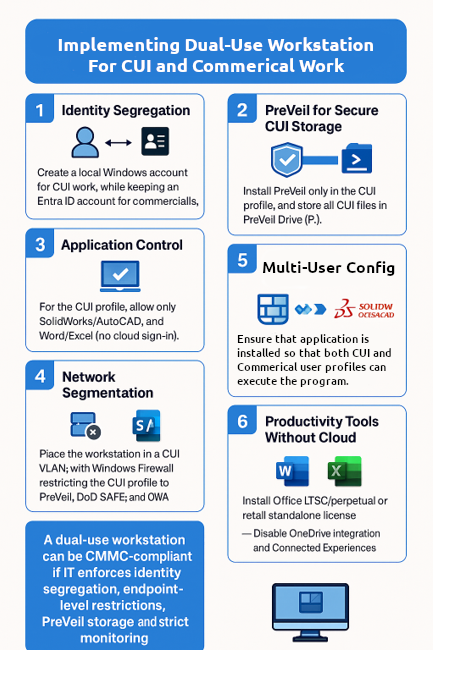
Step 2: Secure Storage With PreVeil
Install PreVeil only inside the CUI profile and require that all CUI files remain within the PreVeil Drive. NTFS permissions ensure the commercial user profile cannot view or access CUI data, preventing accidental exposure or cross-contamination between environments. This storage isolation protects confidentiality and provides measurable, reviewable evidence to support the implementation during assessment.
Step 3: Application Control
Limit software execution to only what is required for CUI processing. AppLocker or WDAC can be used to enforce strict allow-lists so unauthorized software cannot run on the workstation. Only approved offline applications should be permitted such as PreVeil, SolidWorks or AutoCAD, and locally installed productivity tools like Word, Excel, or LibreOffice. This prevents cloud dependent tools, personal productivity software, or unauthorized executables from being introduced into the CUI environment.
Step 4: Network Segmentation
Place the workstation within a dedicated CUI VLAN and enforce outbound traffic restrictions at the firewall based on user identity. Only approved services such as PreVeil and DoD SAFE should be reachable from the CUI profile. This prevents unintended exposure to external networks and commercial cloud infrastructure.
Step 5: Multi-User Licensing Constraints
SolidWorks or AutoCAD must be installed in a way that supports execution from both the CUI and commercial user profiles. The commercial profile may utilize the application, but only the CUI profile is permitted to open and save files to PreVeil storage. This preserves engineering workflow efficiency without compromising CUI isolation.
Step 6: No Cloud Connected Productivity Tools
Use productivity suites that do not rely on Microsoft 365 cloud services or OneDrive synchronization. Office LTSC, perpetual retail licenses, or LibreOffice provide the required functionality without cloud account dependencies. This prevents silent data synchronization, unauthorized cloud paths, and risk of accidental exfiltration.
Step 7: Evidence Preparation
Document every configuration you implement. Capture screenshots, firewall rules, NTFS permissions, AppLocker or WDAC policies, user separation artifacts, diagrams, and administrator validation steps. Evidence must demonstrate that the environment is implemented as described, consistently maintained, and verifiable. The assessor must see that what you say you do is actually done in practice.
Final Takeaway
A dual-use workstation can be CMMC compliant when identity, storage, application, and network boundaries are strictly enforced and continuously maintained. The key is to implement controls intentionally, document them clearly, and support every claim with factual, verifiable evidence during assessment.
-Lamar